FTX Hack or Inside Job? Blockchain Experts Examine Clues and a ‘Stupid Mistake’
The beleaguered crypto exchange FTX suffered a $400 million hack over the weekend, and at least one blockchain expert says the clues are point to a high-level insider who committed an amateur misstep that might have inadvertently revealed their identity.
The attacker appears to have “had access to all the cold wallet storages which he exploited,” Dyma Budorin, co-founder and chief executive of blockchain security auditing firm Hacken, said Monday in an interview with CoinDesk TV.
Hacken investigated blockchain transactions and found that the looter tried to send tether (USDT) stablecoin on the Tron blockchain multiple times unsuccessfully because they didn’t have enough TRX, the Tron network’s native token, in the wallet to pay for transaction fees. So the looter used their verified personal account on crypto exchange Kraken to send 500 TRX to the compromised wallet address to cover the transaction.
“He made a stupid mistake,” Budorin said.
🚨 FTX (@FTX_Official) hot wallets across different networks demonstrated suspicious activity a couple of hours ago
Possible amount of stolen funds can be near $400M
Here are some details
🧶...— Hacken🇺🇦 (@hackenclub) November 12, 2022
Because of Kraken’s “know-your-customer” or KYC measures – part of the anti-money-laundering compliance requirements – and verification process, the exchange had information on who owns the personal wallet the TRX was sent from, revealing the identity behind the exploit.
Hacken immediately contacted Kraken’s security team about the transaction, Budorin said.
“We know the identity of the user,” Nick Percoco, chief security officer of crypto exchange Kraken, said in a tweet Saturday. Percoco added he was told that FTX or the exchange’s founder and former chief executive, Sam Bankman-Fried, will release an official statement.
We know the identity of the user.
— Nick Percoco (@c7five) November 12, 2022
Budorin said that the exploit demonstrated that the way FTX managed its cold wallets was “very poor.”
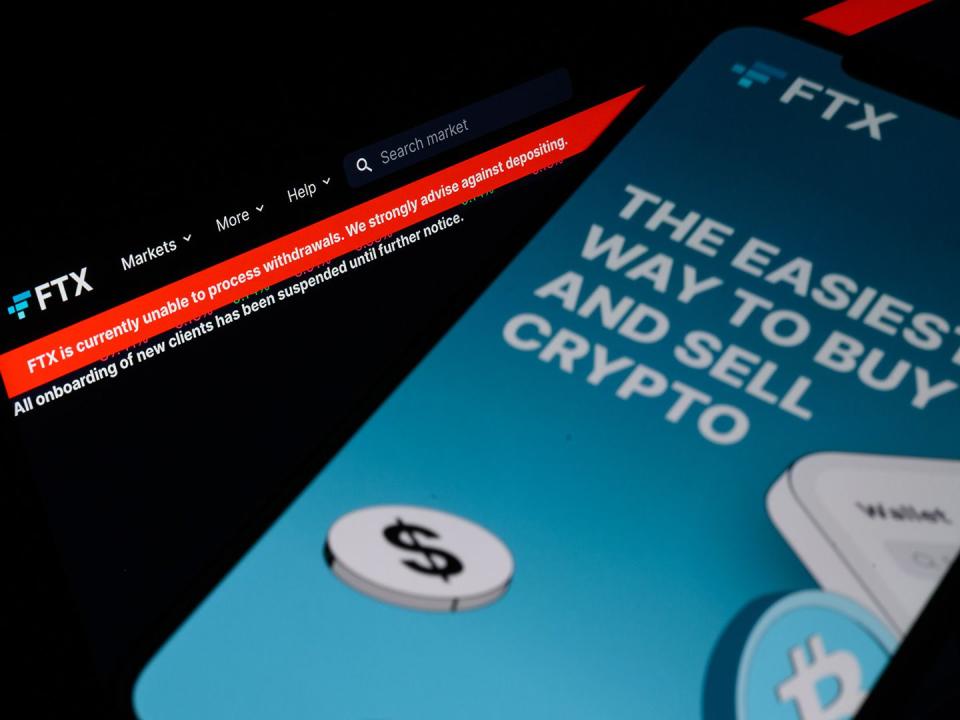
FTX suffered a hack late Friday night, resulting in more than $600 million in digital assets leaving the exchange's wallets in a flurry of withdrawals. FTX's new CEO, John Ray acknowledged that the exchange had been "compromised," and said that it was taking “precautionary steps…to mitigate damage upon observing unauthorized transactions.” Hacken found that one entity, which Budovin suspects to be an insider, siphoned about $400 million from the exchange.
Read more: 'FTX Has Been Hacked': Crypto Disaster Worsens as Exchange Sees Mysterious Outflows Exceeding $600M
New details about the exploit led to speculation on crypto Twitter that possibly FTX owner Sam Bankman-Fried or someone in his close circle could have been behind the exploit, given the access to FTX's cold wallets.
Asked whether Bankman-Fried was the owner of the compromised wallet the exploit originated from, Budorin said that “this is confidential information,” but he added that the wallet’s owner is a U.S. citizen. Budorin did not return CoinDesk’s request for additional comment at publication time on how he obtained information about the hacker’s citizenship and whether Kraken shared any personal data with Hacken of the account’s holder.
A Kraken spokesperson said that the exchange is “in contact with law enforcement, and has frozen Kraken account access to certain funds we suspect to be associated with ‘fraud, negligence or misconduct’ related to FTX,” according to a statement sent in email.
Of course, blockchain-savvy criminals can be sophisticated, so it’s possible that the mistake was a red herring the looter intentionally provided to mislead the investigation – by stirring some confusion.
“It’s very common for a scammer to use a fake KYC (know-your-customer) account so that authorities go chasing the wrong person,” Cryptogle, a blockchain sleuth, told CoinDesk.
Top exchange FTX and its corporate-sibling trading firm Alameda Research were the crown jewels of Bankman-Fried’s crypto empire, which imploded in spectacular fashion last week after a bank run on FTX’s deposits revealed that it had lost billions of dollars of digital assets that belonged to customers.
The whole conglomerate, 138 firms altogether, filed for bankruptcy protection Friday after rescue plans failed, triggering several investigations.
Read more: FTX Files for Bankruptcy Protection in US; CEO Bankman-Fried Resigns
UPDATE (Nov. 14, 21:18): Adds context about FTX's exploit in 9th paragraph.

 Yahoo Finance
Yahoo Finance 