How China steals U.S. secrets
China wants to steal U.S. secrets and is very good at doing so.
“China, from a counterintelligence perspective, represents the broadest, most pervasive, most threatening challenge we face as a country,” FBI Director Christopher Wray told the Aspen Security Forum in July.
A recent U.S. government report titled “Foreign Economic Espionage in Cyberspace” indicates how multifaceted China is when it comes to stealing American intellectual property and U.S. government secrets.
“China has expansive efforts in place to acquire U.S. technology to include sensitive trade secrets and proprietary information,” states the report by the National Counterintelligence and Security Center (NCSC). “It continues to use cyber espionage to support its strategic development goals — science and technology advancement, military modernization, and economic policy objectives.”
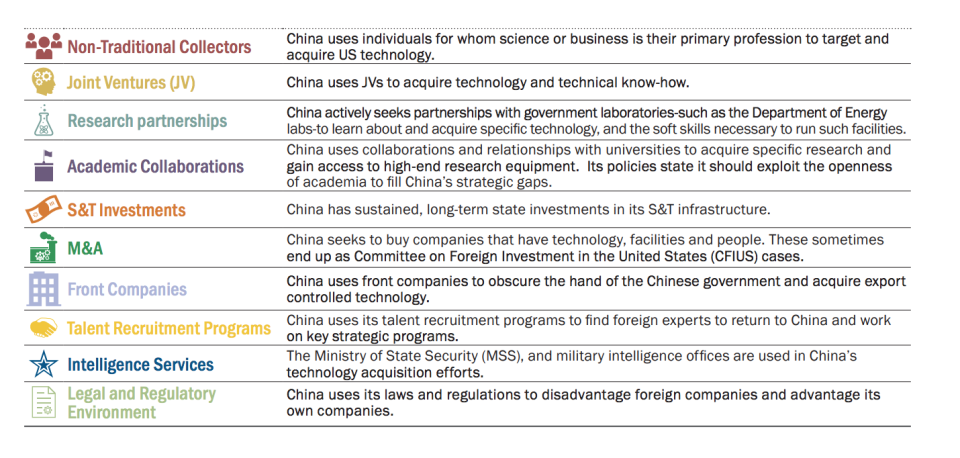
Here’s a look at how the U.S. views China’s strategic goals:

China hopes to further its strategic development goals by using cyber espionage to target “U.S. private industry, focusing on cleared defense contractors or IT and communications firms whose products and services support government and private sector networks worldwide,” the NCSC asserted.
Detailing tactics ranging from engaging academic collaborations to human espionage to hacking, the report shows how Beijing has invested considerable effort to acquire technological know-how from the U.S.
“We believe that China will continue to be a threat to U.S. proprietary technology and intellectual property through cyber-enabled means or other methods,” the report, which also examines Russia and Iran, concludes on China. “If this threat is not addressed, it could erode America’s long-term competitive economic advantage.”
Paul Moore, a former China analyst for the FBI, explained China’s spying mindset with an analogy:
“If a beach were a target, the Russians would send in a sub, frogmen would steal ashore in the dark of night and collect several buckets of sand and take them back to Moscow. The U.S. would send over satellites and produce reams of data. The Chinese would send in a thousand tourists, each assigned to collect a single grain of sand. When they returned, they would be asked to shake out their towels. And they would end up knowing more about the sand than anyone else.”
China has been stealing U.S. intellectual property for decades. Here are some of the recent espionage activities that we know of (organized by type of collection):
Intelligence Services
The most worrying of all is how the Chinese Ministry of State Security (MSS) and military intelligence offices are involved in China’s technology acquisition efforts (in addition to foiling CIA spying efforts).
For example, earlier this year a former U.S. intelligence officer was charged with smuggling information about U.S. military and intelligence issues in exchange for money.
Ron Rockwell Hansen, who had served for 20 years in the U.S. Army (including a few months with the Defense Intelligence Agency), allegedly attended trade conferences on behalf of China and shared the information he had gathered with officials who were connected to Chinese intelligence.
Hansen’s case is just one of many where China targets U.S. citizens to procure U.S. defense secrets, from military aircraft to nuclear systems.

In cases where they can’t entice U.S. intelligence officials or insiders, China also engages in hacking — such as in the case of the F-35 fighter jets.
In 2015, according to documents provided by former U.S. National Security Agency contractor, Edward Snowden, it was revealed that Chinese hackers had stolen data on the F-35 Lightning II joint strike fighter jet from subcontractor Lockheed Martin (LMT).
The case — being one among many more — showed how Chinese hackers are using information mined from U.S. defense contractors to make their own weapons.
The F-35 was turned into China-made stealth fighters such as the J-31 and Chengdu J-20, which has serious national security implications.
Non-Traditional Collectors
According to the NCSC, China uses individuals with a primary profession in science or business to target and acquire U.S. technology.
For example, a General Electric (GE) engineer with ties to China was recently arrested and accused of stealing files related to proprietary power-turbine technology.
Xiaoqing Zheng, a U.S. citizen, was hired by GE to work in its power division in New York. In 2014, GE’s corporate security team detected that Zheng had copied more than 19,000 files from a GE–owned computer to an external storage device. He told GE officials that he had deleted the files — but then repeated the offense in 2017.
The FBI, which worked closely with GE on this case, said Zheng elaborately concealed his actions to avoid detection.

Zheng was arrested in early August 2018.
Silicon Valley, in particular, has become a den of foreign spies targeting various types of information, as detailed by Zach Dorfman in Politico.
“The Chinese just have vast resources,” Kathleen Puckett, who worked counterintelligence in the Bay Area from 1979 to 2007, told Dorfman. “They have all the time in the world, and all the patience in the world. Which is what you need more than anything.”
Last month, U.S. authorities arrested a former Apple Inc. engineer on charges of stealing driverless car secrets for a Chinese startup.
Joint Ventures (JV)
China also uses JVs to acquire technology and technical know-how, according to the report.
Joint ventures are collaborative in theory: Two companies work together to learn from each other’s best practices. But when you’re working with China, it gets murky.
If a foreign firm wants to enter certain industries in China, it usually needs to form a joint venture with a local partner.
And according to a paper by the National Bureau of Economic Research (NEBR) that looked at all international joint ventures in China from 1998 to 2007, the Chinese firms exploit those relationships to gain substantial knowledge from them, which could then be used to replicate the same product.
For example, in a 2017 survey by the U.S.–China Business Council, nearly 20% of American businesses operating in China said that they have been directly asked to transfer technology to a Chinese partner during negotiations.

But it’s difficult to track these trends as “firms have an incentive to keep quiet about these things because part of the quid pro quo is to not complain about what they have to give up for market access,” Thomas Holmes, author of the NBER report, told Yahoo Finance.
Holmes highlighted a case involving German conglomerate Siemens (SIE.DE) as an example of a JV enabling theft of information.
In 2011, the chief executive of French engineering company Alstom (ALO.PA), Patrick Kron, suggested that Siemens may have inadvertently slipped technical know-how to Chinese companies through a high-speed trains partnership.
Kron said then that Alstom was reluctant to enter partnerships in China because he didn’t want to hand over “high-technology components” to Chinese business partners who could use them to turn around and compete against the same companies.
Alstom had previously asserted that 90% of the high-speed rail technology the Chinese are using is derived from their partnerships or equipment that foreign companies had developed.

Mergers and Acquisitions (M&A)
In some cases, China seeks to buy companies outright that have the technology, facilities, and people that it desires. These sometimes end up as Committee on Foreign Investment in the United States (CFIUS) cases, which has the ability to block deals.
But CFIUS has let cases slip through its far too wide fishnet.
Early last year, when a company called Avatar Integrated Systems declared bankruptcy, China swooped hoping to buy one of the company’s previous acquisitions, ATop Tech, which was a chip-designer.
The transaction went through without much fuss from the U.S. government, despite the company making products critical to U.S. military systems. These kinds of deals, particularly with companies that are part of a larger supply chain, would have major national security implications if manipulated or counterfeit Chinese components ended up in military supply chains.
Talent Recruitment Programs
China also uses its talent recruitment programs to find foreign experts to return to China and work on key strategic programs.
China also heavily recruits scientists from abroad enticing them with big paychecks. The country is even offering fast-tracked work visas geared towards Nobel laureates, coaches, and athletes.

Last year, Chinese–American nuclear engineer Allen Ho pled guilty to conspiring to produce “special nuclear material” in China.
Ho was employed as a consultant by a company called CGNPC — China General Nuclear Power Company — and helped them recruit and execute contracts with U.S.-based nuclear engineers to assist in the design and manufacturing of components for nuclear reactors. He also helped facilitate travel to China and payments for the experts in exchange for their services.
Ho is currently serving a two-year prison sentence.
Follow Aarthi and Michael on Twitter.
Read more:

 Yahoo Finance
Yahoo Finance 